Understanding the various types of keys is essential for anyone involved in data management, cryptography, or even basic computer security. Keys play a crucial role in ensuring data integrity, confidentiality, and authenticity. Whether you are a developer, a system administrator, or a security professional, knowing the different types of keys and their applications can significantly enhance your ability to protect and manage data effectively.
What Are Keys?
In the context of data management and security, a key is a piece of information used to control access to data or to perform cryptographic operations. Keys can be used for various purposes, including encryption, decryption, digital signatures, and authentication. They come in different forms and serve different functions, depending on the specific requirements of the application.
Types of Keys in Cryptography
Cryptography relies heavily on keys to secure data. The two primary types of keys in cryptography are symmetric keys and asymmetric keys.
Symmetric Keys
Symmetric keys use the same key for both encryption and decryption. This means that the sender and receiver must share the same key to communicate securely. Symmetric keys are generally faster and more efficient than asymmetric keys, making them suitable for encrypting large amounts of data.
Some common symmetric key algorithms include:
- Advanced Encryption Standard (AES): Widely used for securing sensitive data due to its robustness and efficiency.
- Data Encryption Standard (DES): An older algorithm that has been largely replaced by AES due to vulnerabilities.
- Triple DES (3DES): An enhanced version of DES that applies the DES algorithm three times to improve security.
Asymmetric Keys
Asymmetric keys, also known as public-key cryptography, use a pair of keys: a public key and a private key. The public key is used to encrypt data, while the private key is used to decrypt it. This approach ensures that only the intended recipient can decrypt the data, even if the public key is widely distributed.
Some common asymmetric key algorithms include:
- RSA (Rivest-Shamir-Adleman): One of the most widely used asymmetric algorithms, known for its security and versatility.
- Elliptic Curve Cryptography (ECC): Provides the same level of security as RSA but with shorter key lengths, making it more efficient.
- Digital Signature Algorithm (DSA): Used primarily for creating digital signatures to ensure data integrity and authenticity.
Types of Keys in Databases
In the context of databases, keys are used to uniquely identify records and establish relationships between tables. The primary types of keys in databases include primary keys, foreign keys, and candidate keys.
Primary Keys
A primary key is a unique identifier for a record in a database table. It ensures that each record can be uniquely identified and accessed. Primary keys are essential for maintaining data integrity and preventing duplicate records.
Example of a primary key in a table:
| ID | Name | Age |
|---|---|---|
| 1 | John Doe | 30 |
| 2 | Jane Smith | 25 |
In this example, the “ID” column serves as the primary key, uniquely identifying each record.
Foreign Keys
A foreign key is a field in a table that establishes a link between data in two tables. It acts as a cross-reference between tables, ensuring referential integrity. Foreign keys are crucial for maintaining relationships between different datasets within a database.
Example of a foreign key relationship:
| OrderID | CustomerID | ProductID |
|---|---|---|
| 101 | 1 | 1001 |
| 102 | 2 | 1002 |
In this example, “CustomerID” and “ProductID” are foreign keys that reference the primary keys in the “Customers” and “Products” tables, respectively.
Candidate Keys
A candidate key is a set of one or more columns that can uniquely identify a record in a table. A table can have multiple candidate keys, but only one is chosen as the primary key. Candidate keys are important for ensuring data uniqueness and integrity.
Example of candidate keys:
| EmployeeID | SSN | |
|---|---|---|
| E001 | 123-45-6789 | john.doe@example.com |
| E002 | 987-65-4321 | jane.smith@example.com |
In this example, “EmployeeID,” “SSN,” and “Email” could all serve as candidate keys, but only one would be chosen as the primary key.
Types of Keys in Music
In the realm of music, keys refer to the tonal center around which a piece of music is composed. Understanding the different types of keys is essential for musicians, composers, and music theorists. The two primary types of keys in music are major keys and minor keys.
Major Keys
Major keys are characterized by a bright and uplifting sound. They follow a specific pattern of whole and half steps, creating a distinctive and recognizable melody. Major keys are often associated with happiness, joy, and positivity.
Example of a major key:
C Major: C, D, E, F, G, A, B, C
Minor Keys
Minor keys, on the other hand, have a darker and more somber sound. They also follow a specific pattern of whole and half steps, but with a different interval structure than major keys. Minor keys are often associated with sadness, melancholy, and introspection.
Example of a minor key:
A Minor: A, B, C, D, E, F, G, A
Types of Keys in Physical Security
In physical security, keys are used to control access to buildings, rooms, and other secure areas. The different types of keys in physical security include mechanical keys, electronic keys, and smart keys.
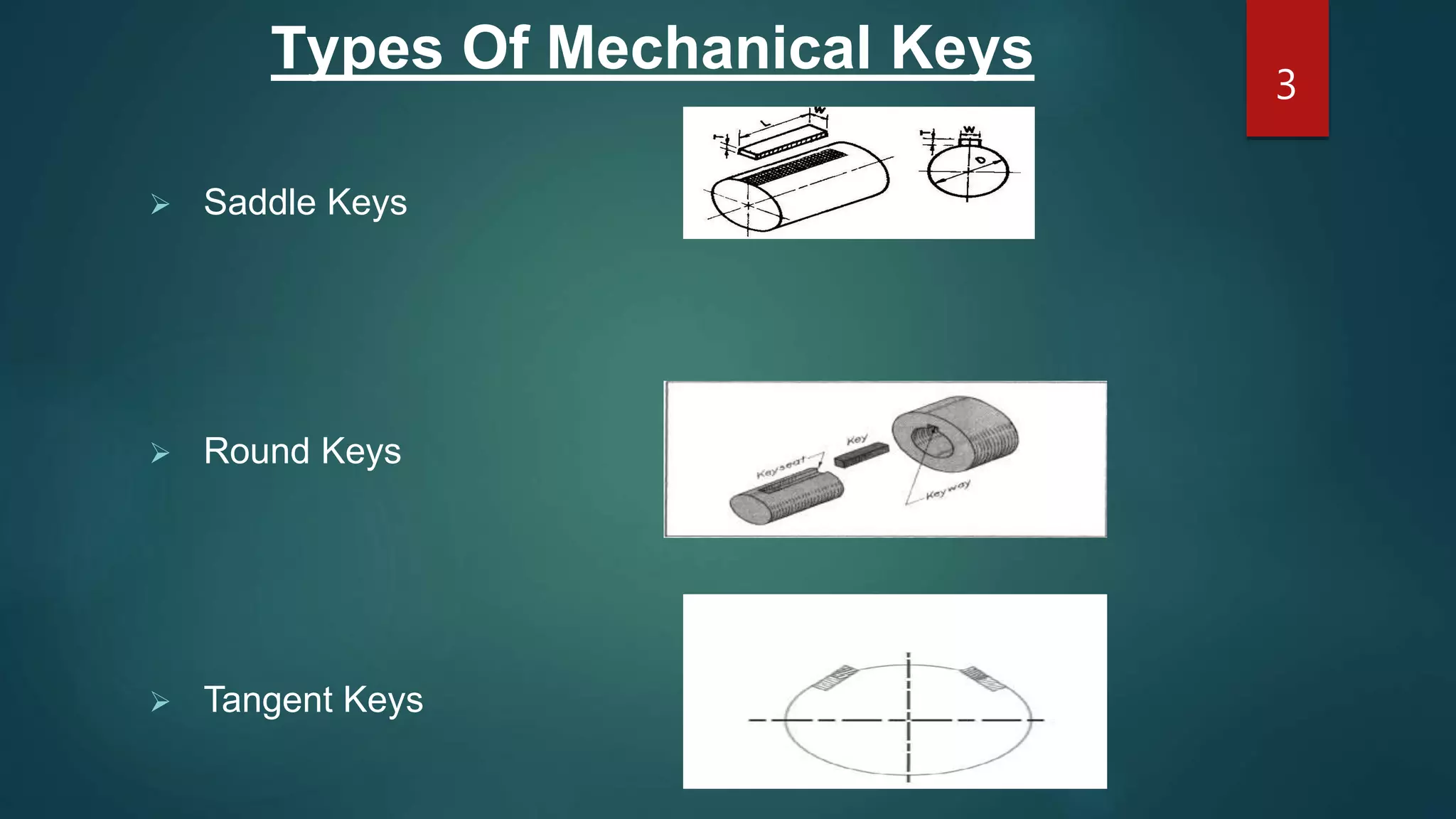
Mechanical Keys
Mechanical keys are the traditional type of keys used to open locks. They consist of a metal blade with cuts or grooves that match the pins inside a lock. Mechanical keys are simple to use but can be easily duplicated, making them less secure for high-security applications.
Electronic Keys
Electronic keys use electronic signals to unlock doors or access control systems. They often come in the form of keycards, fobs, or biometric scanners. Electronic keys offer enhanced security features, such as access logs and remote management, making them suitable for modern security systems.
Smart Keys
Smart keys are advanced electronic keys that use encryption and other security measures to control access. They often include features like proximity sensors, keyless entry, and integration with mobile devices. Smart keys provide the highest level of security and convenience, making them ideal for high-security environments.
🔒 Note: The choice of key type depends on the specific security requirements and the level of protection needed.
In the world of data management, cryptography, music, and physical security, understanding the various types of keys is crucial for effective implementation and security. Whether you are encrypting sensitive data, composing a musical piece, or securing a physical location, knowing the right type of key to use can make all the difference. By leveraging the appropriate keys, you can ensure data integrity, confidentiality, and authenticity, while also enhancing the overall security of your systems and environments.
Related Terms:
- key types explained
- types of keys for locks
- types of keys in technology
- different types of key names
- key types uk
- types of key names