In the realm of digital security and access management, the Ccs Cases Login system plays a pivotal role. This system is designed to provide secure and efficient access to various digital resources, ensuring that only authorized users can gain entry. Understanding the intricacies of the Ccs Cases Login process is crucial for both users and administrators to maintain a robust security posture.
Understanding the Ccs Cases Login System
The Ccs Cases Login system is a comprehensive solution that integrates multiple layers of security to protect sensitive information. It is widely used in various industries, including healthcare, finance, and government, where data security is paramount. The system employs advanced authentication methods to verify the identity of users, ensuring that only authorized personnel can access critical data.
Key Features of the Ccs Cases Login System
The Ccs Cases Login system offers a range of features that enhance its effectiveness and reliability. Some of the key features include:
- Multi-Factor Authentication (MFA): This feature adds an extra layer of security by requiring users to provide multiple forms of identification before gaining access.
- Role-Based Access Control (RBAC): This allows administrators to assign specific roles to users, determining what resources they can access and what actions they can perform.
- Audit Trails: The system maintains detailed logs of all login attempts and activities, providing a comprehensive record for auditing and compliance purposes.
- Single Sign-On (SSO): This feature enables users to log in once and gain access to multiple applications without needing to re-enter their credentials.
Setting Up the Ccs Cases Login System
Setting up the Ccs Cases Login system involves several steps, each crucial for ensuring the system's security and functionality. Below is a detailed guide to help you through the process:
Step 1: Installing the System
The first step is to install the Ccs Cases Login system on your server. This process typically involves downloading the installation package and following the on-screen instructions. Ensure that your server meets the system requirements for optimal performance.
Step 2: Configuring the Database
Once the system is installed, the next step is to configure the database. This involves setting up the database schema and importing any necessary data. The configuration process may vary depending on the database management system you are using.
Step 3: Setting Up User Accounts
After configuring the database, you need to set up user accounts. This includes creating administrator accounts and defining user roles and permissions. It is essential to follow best practices for password management to ensure the security of user accounts.
Step 4: Enabling Multi-Factor Authentication
To enhance the security of the Ccs Cases Login system, it is recommended to enable Multi-Factor Authentication (MFA). This can be done through the system's administration panel, where you can configure the MFA settings and choose the authentication methods to be used.
Step 5: Configuring Audit Trails
Audit trails are crucial for monitoring and auditing user activities. Configure the audit trail settings to ensure that all login attempts and activities are logged. This will provide a comprehensive record for compliance and security purposes.
Step 6: Implementing Single Sign-On (SSO)
Single Sign-On (SSO) simplifies the login process for users by allowing them to access multiple applications with a single set of credentials. Configure SSO settings to integrate the Ccs Cases Login system with other applications and services.
🔒 Note: Ensure that all configurations are tested thoroughly to identify and resolve any potential issues before deploying the system to production.
Best Practices for Using the Ccs Cases Login System
To maximize the effectiveness and security of the Ccs Cases Login system, it is essential to follow best practices. Here are some key recommendations:
- Regularly Update the System: Keep the system up-to-date with the latest security patches and updates to protect against vulnerabilities.
- Conduct Regular Audits: Perform regular audits of user activities and system logs to detect any suspicious behavior.
- Implement Strong Password Policies: Enforce strong password policies to ensure that user passwords are complex and secure.
- Train Users on Security Best Practices: Educate users on the importance of security and best practices for protecting their credentials.
- Monitor for Unusual Activity: Continuously monitor the system for unusual activity and take immediate action if any anomalies are detected.
Common Issues and Troubleshooting
Despite its robustness, the Ccs Cases Login system may encounter issues from time to time. Here are some common problems and their solutions:
Issue 1: Forgotten Password
If a user forgets their password, they can use the password recovery feature to reset it. Ensure that the password recovery process is secure and that users are prompted to create a strong new password.
Issue 2: MFA Not Working
If Multi-Factor Authentication (MFA) is not working, check the configuration settings and ensure that the authentication methods are correctly set up. Verify that the user's device supports the chosen MFA method.
Issue 3: SSO Integration Problems
If there are issues with SSO integration, review the configuration settings and ensure that the Ccs Cases Login system is correctly integrated with the other applications. Check for any compatibility issues and update the system if necessary.
🛠️ Note: Always refer to the system's documentation for detailed troubleshooting steps and solutions.
Enhancing Security with the Ccs Cases Login System
The Ccs Cases Login system offers several advanced features to enhance security. Here are some key enhancements:
Advanced Threat Detection
The system can be configured to detect and respond to advanced threats, such as brute-force attacks and phishing attempts. Implementing advanced threat detection mechanisms can significantly improve the system's security posture.
Encryption
Data encryption is a crucial aspect of security. Ensure that all data transmitted and stored within the Ccs Cases Login system is encrypted to protect it from unauthorized access.
Regular Security Audits
Conducting regular security audits helps identify vulnerabilities and potential threats. Use the audit trail feature to review user activities and system logs, and take corrective actions as needed.
User Education
Educating users on security best practices is essential for maintaining a secure environment. Provide training sessions and resources to help users understand the importance of security and how to protect their credentials.
Case Studies: Successful Implementation of the Ccs Cases Login System
Several organizations have successfully implemented the Ccs Cases Login system to enhance their security and access management. Here are a few case studies:
Case Study 1: Healthcare Provider
A large healthcare provider implemented the Ccs Cases Login system to secure patient data. By using MFA and RBAC, they ensured that only authorized personnel could access sensitive information. The system's audit trail feature helped them comply with regulatory requirements and maintain a high level of security.
Case Study 2: Financial Institution
A financial institution used the Ccs Cases Login system to protect customer data and transactions. The implementation of SSO simplified the login process for users, while advanced threat detection mechanisms helped identify and mitigate potential threats. The system's encryption features ensured that all data was secure.
Case Study 3: Government Agency
A government agency deployed the Ccs Cases Login system to manage access to critical systems and data. The system's role-based access control and audit trail features helped them maintain a secure and compliant environment. Regular security audits and user education programs further enhanced the system's effectiveness.
Future Trends in Access Management
The field of access management is continually evolving, with new technologies and trends emerging to enhance security and efficiency. Some of the future trends in access management include:
- Biometric Authentication: The use of biometric data, such as fingerprints and facial recognition, for authentication is becoming more prevalent. This method provides an additional layer of security and convenience for users.
- Artificial Intelligence (AI): AI can be used to detect and respond to threats in real-time, enhancing the system's ability to protect against advanced attacks.
- Blockchain Technology: Blockchain can be used to create a secure and immutable record of user activities, providing a high level of transparency and security.
- Zero Trust Architecture: This approach assumes that threats can exist both inside and outside the network, requiring continuous verification of user identities and access rights.
As these trends continue to develop, the Ccs Cases Login system will likely incorporate new features and technologies to stay ahead of emerging threats and meet the evolving needs of users.
In conclusion, the Ccs Cases Login system is a robust and comprehensive solution for secure access management. By understanding its key features, following best practices, and staying informed about future trends, organizations can enhance their security posture and protect sensitive information effectively. The system’s advanced authentication methods, role-based access control, and audit trail features make it a valuable tool for maintaining a secure digital environment. Regular updates, audits, and user education are essential for maximizing the system’s effectiveness and ensuring ongoing protection against threats.
Related Terms:
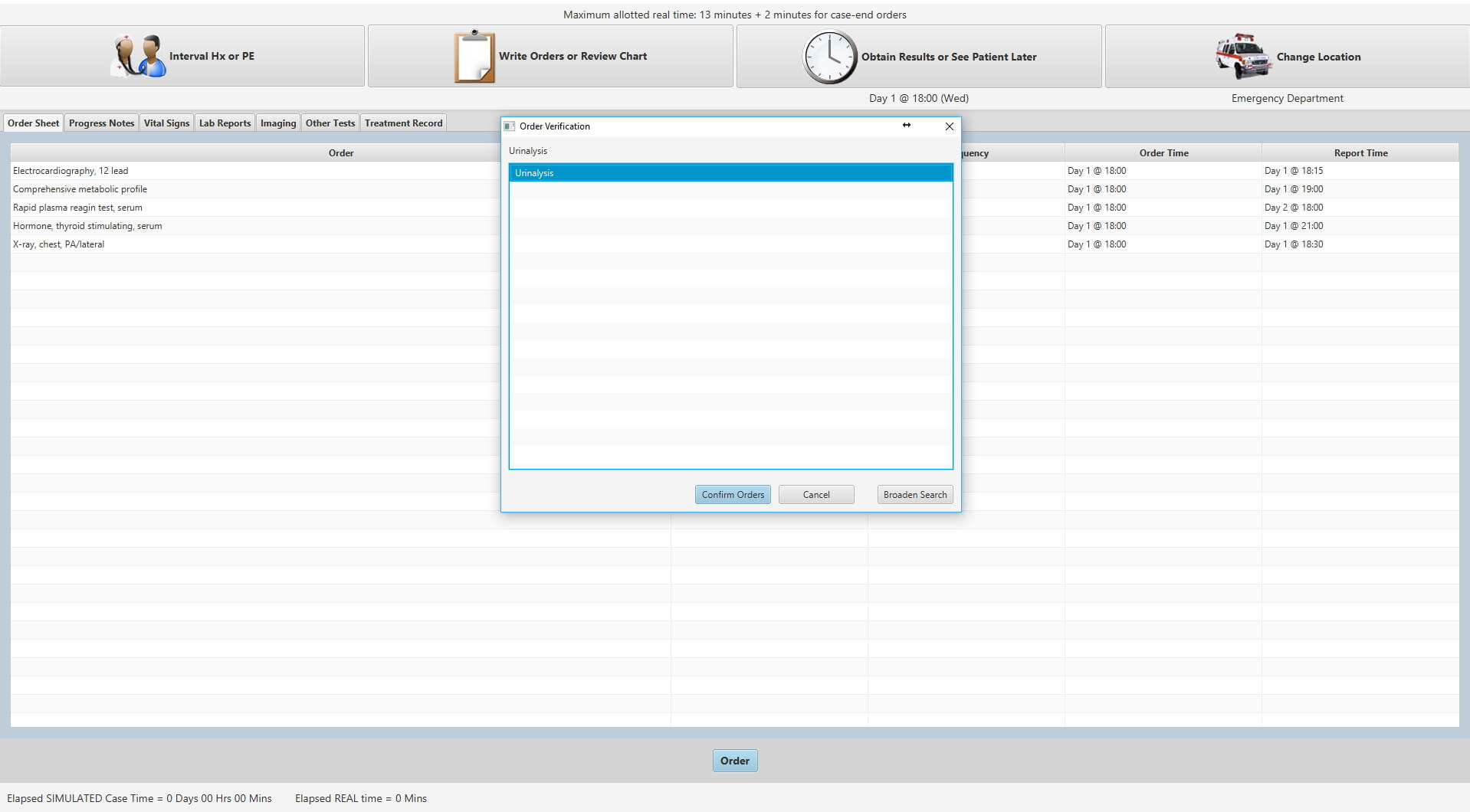
- how to do ccs cases
- ccs cases demo
- dcs caseline login
- ccscases.com
- ccs login step 3
- ccs cases step 3 reddit