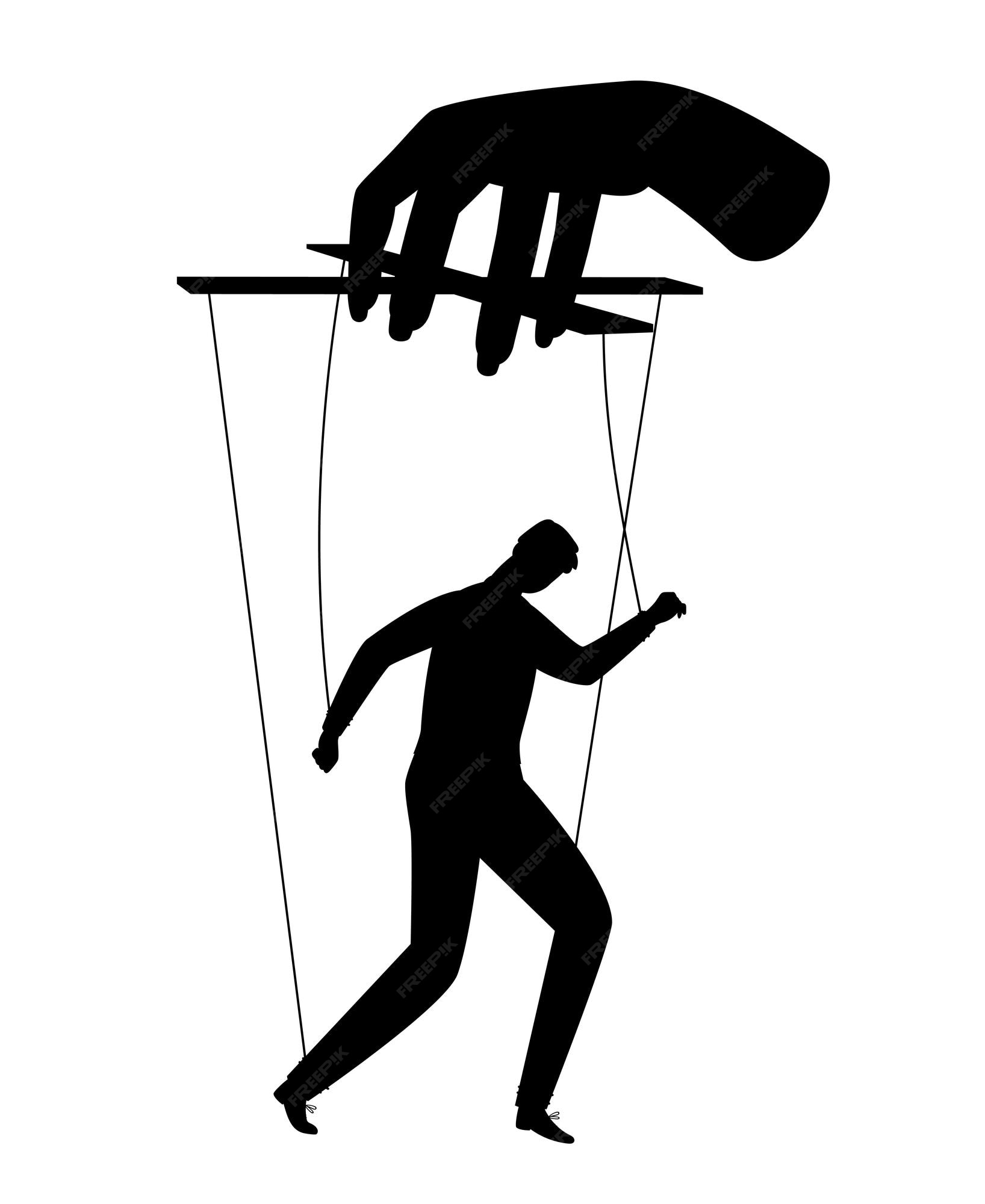
In the world of cybersecurity, the concept of "Stringing A Puppet" refers to the manipulation of a system or network to perform actions under the control of an attacker. This technique is often used in advanced persistent threats (APTs) and other sophisticated cyber-attacks. Understanding how to detect and mitigate these threats is crucial for protecting sensitive information and maintaining the integrity of digital systems.
Understanding Stringing A Puppet
Stringing A Puppet involves the use of various techniques to gain control over a target system. This can include:
- Exploiting vulnerabilities in software or hardware.
- Using social engineering to trick users into granting access.
- Deploying malware that can execute commands remotely.
Once control is established, attackers can use the compromised system to:
- Steal sensitive data.
- Launch further attacks on other systems.
- Disrupt operations and cause financial or reputational damage.
Common Techniques Used in Stringing A Puppet
Attackers employ a variety of methods to string a puppet. Some of the most common techniques include:
Exploiting Software Vulnerabilities
Software vulnerabilities are often the entry point for attackers. These vulnerabilities can be in operating systems, applications, or even firmware. Attackers use tools like exploit kits to automatically scan for and exploit these weaknesses.
Social Engineering
Social engineering involves manipulating people into performing actions or divulging confidential information. This can be done through phishing emails, fake websites, or even direct communication. Once an attacker gains access through social engineering, they can string the puppet to perform malicious actions.
Malware Deployment
Malware is a broad term that includes viruses, worms, Trojan horses, ransomware, and spyware. Once malware is deployed on a system, it can provide attackers with remote control, allowing them to string the puppet and execute commands as needed.
Detecting Stringing A Puppet Attacks
Detecting Stringing A Puppet attacks requires a multi-layered approach. Here are some key strategies:
Network Monitoring
Continuous network monitoring can help detect unusual activity that may indicate a puppet is being controlled. This includes monitoring for:
- Unexpected outbound traffic.
- Unusual login attempts.
- Changes in network topology.
Endpoint Security
Endpoint security solutions can detect and block malware that might be used to string a puppet. These solutions often include:
- Antivirus software.
- Intrusion detection systems (IDS).
- Endpoint detection and response (EDR) tools.
User Education
Educating users about the risks of social engineering and other attack vectors is crucial. Regular training sessions can help users recognize and avoid phishing attempts and other social engineering tactics.
Mitigating Stringing A Puppet Attacks
Mitigating Stringing A Puppet attacks involves a combination of technical controls and best practices. Here are some effective strategies:
Patch Management
Regularly updating software and systems to patch known vulnerabilities is essential. This includes:
- Operating systems.
- Applications.
- Firmware.
Access Controls
Implementing strong access controls can limit the damage caused by a compromised system. This includes:
- Using multi-factor authentication (MFA).
- Implementing the principle of least privilege.
- Regularly reviewing and updating access permissions.
Incident Response Planning
Having a well-defined incident response plan can help organizations quickly detect and respond to Stringing A Puppet attacks. This plan should include:
- Steps for identifying and containing the threat.
- Procedures for eradicating the threat.
- Plans for recovering from the attack.
Case Studies of Stringing A Puppet Attacks
To better understand the impact of Stringing A Puppet attacks, let's examine a few case studies:
Stuxnet
Stuxnet is a notorious example of a Stringing A Puppet attack. This malware targeted industrial control systems, specifically those used in Iran's nuclear program. By exploiting vulnerabilities in Windows and Siemens software, Stuxnet was able to manipulate the control systems and cause physical damage to centrifuges.
NotPetya
NotPetya is a ransomware attack that spread rapidly through networks, encrypting files and demanding ransom payments. The malware used a combination of techniques, including exploiting vulnerabilities in accounting software and using stolen credentials to move laterally within networks. The attack caused billions of dollars in damage and disrupted operations for many organizations.
Preventing Future Stringing A Puppet Attacks
Preventing future Stringing A Puppet attacks requires a proactive approach. Here are some key strategies:
Regular Security Audits
Conducting regular security audits can help identify vulnerabilities and weaknesses in your systems. These audits should include:
- Vulnerability assessments.
- Penetration testing.
- Compliance checks.
Threat Intelligence
Using threat intelligence can provide insights into emerging threats and attack vectors. This information can be used to:
- Update security policies.
- Improve detection capabilities.
- Enhance incident response plans.
Employee Training
Continuous employee training is essential for maintaining a strong security posture. This includes:
- Regular security awareness training.
- Phishing simulations.
- Workshops on best security practices.
🔒 Note: Regularly updating security policies and procedures is crucial for maintaining an effective defense against Stringing A Puppet attacks.
Stringing A Puppet attacks are a significant threat to organizations of all sizes. By understanding the techniques used in these attacks, implementing effective detection and mitigation strategies, and staying proactive in your security efforts, you can protect your systems and data from these sophisticated threats. The key is to remain vigilant, continuously update your defenses, and be prepared to respond quickly to any potential breaches.
Related Terms:
- parts of a marionette puppet
- doll controlled by strings
- parts of a string puppet
- how to string a marionette
- marionette puppets
- pelham puppets made simple